SEQUOIA TOUCH-SCREEN VOTING MACHINES HACKED, FOUND VULNERABLE TO VOTE-FLIPPING BY PRINCETON UNIVERSITY!
Guest Blogged by John Gideon, with additional reporting by Brad Friedman
“We can take a version of Sequoia’s software program and modify it to do something different — like appear to count votes, but really move them from one candidate to another. And it can be programmed to do that only on Tuesdays in November, and at any other time. You can’t detect it,” Princeton’s Professor of Computer Science Andrew Appel explains in New Jersey’s Star-Ledger today.
Like Diebold’s touch-screen machines before them, Sequoia’s voting machines have now been found to be hackable in seconds by a Princeton University professor who says the systems could be “easily…rigged to throw an election.” Someone may wish to let the folks in Riverside County, CA, know since County Supervisors there recently issued a “thousand to one” bet that their Sequoia voting systems couldn’t be manipulated.
 In the same report, it was revealed that an attorney has filed suit, claiming the Sequoia AVC Advantage Direct Recording Electronic (DRE) voting machines used in 18 of New Jersey’s 21 counties were never reviewed by the state before they were improperly certified for use and that Princeton’s Appel was able to acquire five Sequoia voting machines for only $86. The same machines were recently purchased by the state for $8,000 apiece.
In the same report, it was revealed that an attorney has filed suit, claiming the Sequoia AVC Advantage Direct Recording Electronic (DRE) voting machines used in 18 of New Jersey’s 21 counties were never reviewed by the state before they were improperly certified for use and that Princeton’s Appel was able to acquire five Sequoia voting machines for only $86. The same machines were recently purchased by the state for $8,000 apiece.
According to the Star-Ledger…
“There is zero documentation — no proof whatsoever — that any state official has ever reviewed Sequoia machines,” Venetis, co-director of the Rutgers Constitutional Litigation Clinic, said in an interview. “This means you cannot use them. … These machines are being used to count most of the votes in the state without being tested in any way, shape or form.”
 Venetis argues that the state certification is in violation of NJ state law which says such systems must “correctly register and accurately count all votes cast,” be “of durable construction” to be used “safely, efficiently, and accurately.”
Venetis argues that the state certification is in violation of NJ state law which says such systems must “correctly register and accurately count all votes cast,” be “of durable construction” to be used “safely, efficiently, and accurately.”
The lack of documentation and testing, however, is hardly the only problem, as reported by the paper today. “Had the machines been tested,” Election Integrity advocates have found, “they would have proved to be a hacker’s dream.”
Princeton Computer Science Professor Andrew Appel revealed that he bought 5 of the Advantage voting machines from an on-line government equipment clearinghouse for a total of $86. Virtually identical machines were bought in 2005 by Essex County New Jersey for $8,000 per machine.
“Appel had to submit only minimal personal information and a cashier’s check to close the deal,” the Star-Ledger reports. He and his team then put the 5 machines to good use…
“We can take a version of Sequoia’s software program and modify it to do something different — like appear to count votes, but really move them from one candidate to another. And it can be programmed to do that only on Tuesdays in November, and at any other time. You can’t detect it,” Appel said last week.
And what does Sequoia systems vaunted crisis-management team have to say for itself?
While promising to look into Appel’s claims, Sequoia’s Michelle Shafer asserted that hacking scenarios are unlikely. “It’s not just the equipment. There are people and processes in place in the election environment to prevent tampering and attempts at tampering,” she said.
Appel counters:
Then, he said, it will be fairly simple for anyone with bad intentions and a screwdriver to swap Sequoia’s memory chips for reprogrammed ones.
Of course, this is not the first time that Sequoia’s “tamperproof products” have been found to be highly tamperable.
In March of 2006, just prior to the Pennsylvania’s Primary Election, Carnegie Mellon University’s Dr. Michael Shamos, — a long-time advocate of electronic, touch-screen voting — accidentally “hacked” a Sequoia system during a demonstration of the system’s “invulnerability” to tampering. Shamos was in charge of testing systems for the state.
As well, last November, just days before the General Election, in a stunning report by The BRAD BLOG we revealed the “yellow button” on the back of every Sequoia touch-screen machine which, when pressed once in a simple sequence, places the machine into “manual mode,” allowing anybody to cast as many votes as che or she wishes on that machine.
In Riverside County, CA, just before the end of last year, County Supervisor Jeff Stone challenged Election Integrity advocates during a public, video-taped meeting to bring a hacker in to try and manipulate the county’s Sequoia voting systems. Riverside was the first county in the country to move to touch-screen voting in the late 90’s. Election Integrity advocates on the ground there have been challenging that decision ever since.
Though noted computer security expert Harri Hursti, who has hacked several Diebold systems, quickly agreed to meet Stone’s “thousand to one” challenge, Stone has been balking ever since. So far, he has failed to allow Hursti and the Election Integrity advocates from DFA-Temecula Valley to take him up on his ill-considered challenge, citing unsubstantiated concerns about state law and universally attempting to establish “ground rules” which have been dismissed as unrealistic by both Hursti and a number of internationally recognized computer scientists and security experts.
We suspect there will be much fallout from this latest chapter in New Jersey. Stay tuned…
UPDATE: Princeton Professor Appel has described the act of purchasing the Sequoia Advantage machines and what he found on opening the machines and the actions that students are taking in his blog “How I bought used voting machines on the Internet”. His blog includes the following:
“The vote counting instructions in each voting machine are written into integrated circuit chips during the manufacturing process. These chips are incorporated into each machine’s circuit boards. Access to the machine should be limited by administrative procedures and is also limited by the physical design of the machines. Design features include door locks and a numbered seal on the CPU cover.”
I found this to be incorrect, with respect to the machines delivered to me. I did not have to remove any seals, whether of tape, plastic, or wire. The sheet-metal panel covering the computer circuit board is the only component I found that could possibly be described as a “CPU cover”, and it had no numbered seal. (If there ever was a numbered seal holding the CPU cover down, then Buncombe County’s technicians would have to remove it and replace it every time they change the four AA batteries on the motherboard!)
The AVC Advantage can be easily manipulated to throw an election because the chips which control the vote-counting are not soldered on to the circuit board of the DRE. This means the vote-counting firmware can be removed and replace with fraudulent firmware. Under the sheet-metal panel (the “CPU cover”), I found the circuit board containing computer chips, other electronic chips, and four chips that–unlike most of the chips on the circuit board which are soldered in place–are mounted in sockets so that they can be removed and replaced. These are ROM (read-only memory) chips that hold the computer program (firmware) that operates the voting logic. These chips are not held in place by any seals. They can be removed using an ordinary screwdriver and they (or other ROM chips containing other firmware) can be replaced simply by pressing them into place. You can see the ROM chips in the picture above; they have the white labels pasted onto them, and you can see me in the process of prying one loose with a screwdriver.
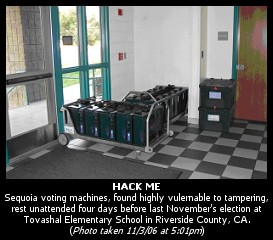
Like the purchasers of all the other lots sold by Buncombe County, I am now at leisure to examine the contents of the firmware on the ROM chips, and to modify it. If I had the inclination to cheat in an election (which I do not) I could prepare a modified version of the firmware that subtly alters votes as the votes are cast, with no indication of the alteration made visible to the voter. I would write this modified firmware onto new ROM chips. Then, if I had access to one of New Jersey’s voting machines (for example, in an elementary school or firehouse where it is left unattended the night before an election), I could open the door of the machine, unscrew 10 screws, replace the legitimate ROM chips with my own fraudulent ones, reinstall the cover panel with its 10 screws, and close the door of the machine.
by John Gideon for The BRAD BLOG


